In the dynamic landscape of enterprise operations, where every click and keystroke can potentially expose sensitive data to unseen threats, the need for robust network security management software is rising day by day.
In this ever-evolving cyber battleground, enterprises are seeking a shield against the myriad of risks lurking in the shadows of the internet. But fear not, for the solution lies not in generic off-the-shelf software but in tailored, bespoke creations crafted with your unique challenges in mind.
Tailored network security management software could be your digital fortress, meticulously designed to safeguard your data assets, monitor network traffic with unwavering vigilance, and swiftly respond to any breach attempts with the precision of a cyber-savvy sentinel.
In this blog, you’ll explore the frontier of network security management software development, unraveling the mysteries of custom-built enterprise solutions that adapt and evolve alongside your business’s needs. So, if you’re ready to arm yourself with the ultimate defense against digital threats, join us on this journey and discover how our customized software development services can empower your enterprise to navigate the digital realm with confidence and resilience.
What is Network Security Management Software?
It is a sophisticated tool that can be designed to automate the crucial task of safeguarding both physical and virtual network devices, along with the sensitive data traversing through them, against cyber threats. With enterprise software development services, you can seek a comprehensive solution that provides robust protection to your digital infrastructure.
In essence, network security management software can act as a proactive shield, continuously monitoring and fortifying your network perimeter to prevent unauthorized access, data breaches, and other malicious activities. While that’s just basic, if you leverage tailored software development services and get advanced algorithms and security protocols integrated, the tool could ensure that the integrity and confidentiality of your critical assets stay intact. This smart move will allow you to operate with confidence in today’s increasingly complex cybersecurity landscape.
Moreover, network security management software streamlines the security management process, reducing manual intervention and enhancing operational efficiency. It empowers organizations to stay ahead of evolving threats and compliance requirements, thereby safeguarding their reputation and bottom line.
Understanding the Urgency of Investing in Custom Network Security Management Systems
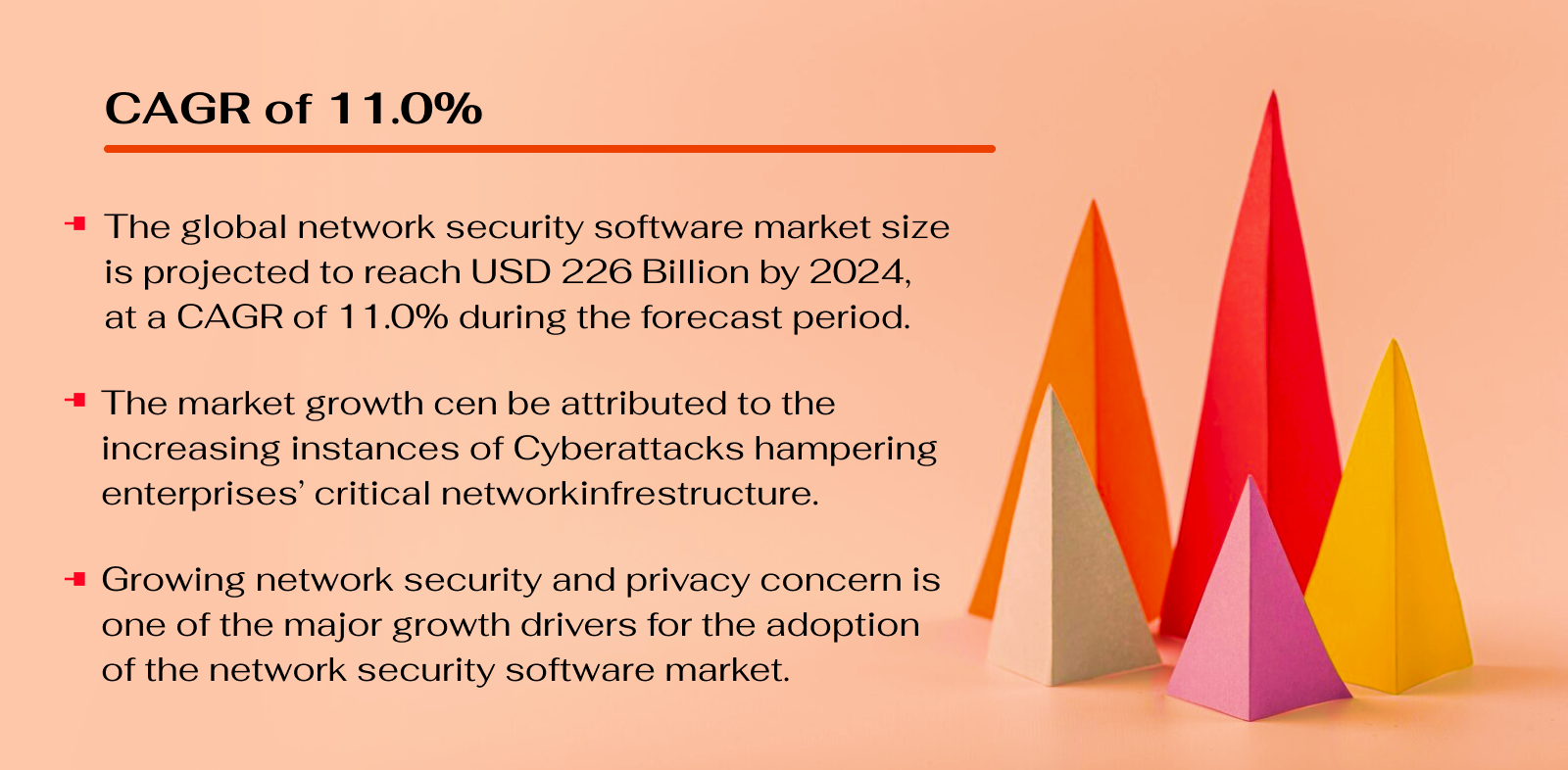
Source: Markets and Markets
Use Cases of Network Security Management Software
An advanced tool for making your company network secure is not an option anymore. With the rising danger of cyber threats, safeguarding your organization’s network infrastructure should be your first priority, irrespective of the domain you operate in. Now, if you’re thinking about how this tool will actually protect, here are some of its common use cases that will blow your mind and keep your worries regarding security at bay.
Monitoring Network Traffic
Network security management software can continuously monitor incoming and outgoing network traffic to detect any suspicious or unauthorized activities, such as malware infections, intrusions, or data breaches.
Also Read: Customizing Excellence: Tailored Network Performance Monitoring Solutions
Vulnerability Assessment
It can conduct regular vulnerability assessments and scans to identify weaknesses in the network infrastructure, such as outdated software, misconfigurations, or unpatched systems, which could be exploited by attackers.
Intrusion Detection and Prevention
When sought through digital transformation services, this software can come with built-in intrusion detection and prevention systems (IDPS). These functionalities help detect and block malicious activities in real-time, including intrusion attempts, denial-of-service (DoS) attacks, and suspicious behavior from both internal and external sources.
Firewall Management
Network security management software can facilitate centralized management of firewalls deployed across the network, ensuring consistent enforcement of security policies, access control rules, and traffic filtering to prevent unauthorized access and data exfiltration.
Security Policy Management
Tailored software for network security management can also help define, enforce, and manage security policies and compliance requirements across the entire network infrastructure, ensuring adherence to industry regulations and organizational standards.
Security Incident Response
In the event of a security incident or breach, cutting-edge network security management software, including AI surveillance software, can provide incident response capabilities, such as alerting administrators, logging incident details, initiating automated responses, and facilitating forensic analysis to mitigate the impact and prevent recurrence.
User Authentication and Access Control
In most cases, such a solution can manage user authentication processes, access control mechanisms, and identity management solutions to ensure that only authorized users and devices can access network resources, applications, and sensitive data.
Encryption and Data Protection
The software can come in handy when you want to implement encryption protocols and data protection mechanisms to secure sensitive information transmitted over the network. This prevents eavesdropping, interception, or unauthorized access to confidential data.
Compliance Reporting and Auditing
Network Segmentation and Isolation
The network planning software can manage network segmentation and isolation strategies to compartmentalize critical assets, segregate sensitive data, and limit the lateral movement of threats within the network, reducing the attack surface and containing potential breaches.
Solve Multiple Security Concerns with Tailored Network Security Management Software.
Types of Businesses That Can Benefit from Tailored Network Security Management Software
If you have a complex network architecture, you should consider network management software development. While most of the time, this software covers the security needs of a company, many times, an added layer of protection is required, especially if your network is prone to malware attacks and cybersecurity threats. In such cases, it’s pivotal to keep the digital defense of your business airtight through tailored network security management solutions. And don’t worry about it resonating with your business needs. Tailored solutions can fit your needs and goals somewhat perfectly. Some key businesses that can use and benefit from this software are as follows-
Small Businesses
These are the mom-and-pop shops, the startups, the local heroes! Tailored network security management software gives them a digital shield against cyber threats, helping them protect their customer data and keep their operations humming along smoothly.
Medium-Sized Enterprises
Picture the bustling hive of activity—medium-sized enterprises are where the action’s at! With tailored network security management software, they can streamline their security operations, scale up their defenses, and stay one step ahead of cyber villains.
Large Corporations
These are the titans of the industry! A tailored solution to manage the security of their network is like having a fortress around their digital empire, shielding them from even the most sophisticated cyber threats. With this software, large corporations can centralize their security operations and gain full visibility into their sprawling networks.
E-commerce Businesses
Welcome to the digital marketplace! E-commerce businesses live and breathe online, which means they’re constantly under siege from cyber predators. Therefore, for these businesses, this tool can act as their digital bouncer, keeping out the riff-raff and protecting their customers’ sensitive information.
Financial Institutions
Money makes the world go ’round, right? That also makes financial institutions prime targets for cyber attacks. But fear not! If you fall into this category, then start off your journey of having tailored network security management software with technology consulting services. This way, you can plan out everything carefully, even if you’re looking for a digital vault with layers upon layers of security measures.
Healthcare Organizations
From hospitals to clinics, healthcare organizations hold some of our most sensitive information. A customized solution for security management can be their digital guardian, protecting patient data and ensuring compliance with strict healthcare regulations.
Government Agencies
These are the stewards of public trust, tasked with safeguarding sensitive information and critical infrastructure. Integration of this software can help them stay ahead of cyber threats, protect citizen data, and ensure the integrity of government systems and services.
Educational Institutions
Schools, colleges, and universities are not immune to cyber threats. A fine-tuned network security management solution can enable educational institutions to protect student records, research data, and intellectual property, ensuring a safe and secure learning environment for students and faculty alike.
Seek Specialized Network Security Management Software Development Services for Your Unique Business Needs.
Advanced Features to Consider in Your Network Security Management Software
When it comes to safeguarding a modern enterprise’s digital infrastructure, having technologies like AI, ML, IoT, and more backing your network’s security is like having a vigilant guardian that keeps a watchful eye over all your digital assets, ensuring they stay safe from cyber threats. So, what advanced features should such software possess to meet the diverse needs of your business? Let’s explore.
 AI-Powered Threat Detection
AI-Powered Threat Detection
Imagine having a super-smart digital watchdog constantly scanning your network traffic. It’s like having a highly-trained security guard who never sleeps, spotting and stopping cyber threats before they can cause any harm. With this feature integrated through AI development services, you can seek network security management software that keeps your digital assets always under strong surveillance.
 ML-Driven Behavioral Analysis
ML-Driven Behavioral Analysis
This feature is like having a detective on your team, analyzing the behavior of everyone and everything on your network. It can spot anomalies that might indicate a security breach, like unusual login patterns or suspicious data transfers. With this insight, you can catch threats before they escalate into full-blown disasters.
 IoT Integration
IoT Integration
In today’s connected world, every device is a potential entry point for cyber attacks. With IoT integration services, your security software could extend its protective reach to cover everything from smart thermostats to industrial sensors. It’s like adding an extra layer of security to every device on your network, keeping them safe from cyber threats.
 Data Analytics for Predictive Insights
Data Analytics for Predictive Insights
This feature is like having a crystal ball for cyber threats. By analyzing data from your network, data analytics and predictive analytics are technologies that run in the background to identify patterns and trends that might indicate a future attack. Their inclusion in your network security management software means getting an early heads-up every time a potential threat is about to hit. The best part? You can have an analytics dashboard to view it all in your software, allowing you to shore up your defenses before it’s too late.
 Automation for Rapid Response
Automation for Rapid Response
When a cyber-attack strikes, every second counts. With automation, your software can spring into action instantly, containing the threat before it spreads. It’s like having a team of cyber first responders ready to leap into action at a moment’s notice, minimizing the impact of any security incident.
 Enhanced User Behavior Analysis
Enhanced User Behavior Analysis
Humans are often the weakest link in cybersecurity. Including this feature in your network security management software, you can identify risky behavior, like employees accessing sensitive data they shouldn’t or clicking on suspicious links. It’s like having a safety net to catch potential security slip-ups before they turn into disasters.
 AI-Powered Compliance Monitoring
AI-Powered Compliance Monitoring
Compliance regulations can be a headache, but with AI, it’s a breeze. This feature ensures your organization stays in line with regulations by constantly monitoring your operations for any potential violations. It’s like having a compliance expert on call 24/7, keeping you on the right side of the law.
 Advanced Threat Intelligence
Advanced Threat Intelligence
Cyber threats are constantly evolving and becoming hard to avoid. But by tapping into a network of threat intelligence through your software, you and your team can stay updated on the latest threats and vulnerabilities. It’s like having a team of cyber spies feeding you real-time intel on potential threats so you can stay ahead of the game.
Get a Feature-Rich and Advanced Network Security Management Software With Us.
Steps for Network Security Management Software Development
Once you’ve made up your mind to seek a tailored solution for your network’s security management, it’s time to assemble a dream team of tech experts. And why wander around when you can have this dream team in one place by collaborating with an expert software development company? This way, you will only need to coordinate and cooperate with these experts while they manage all the intricacies and core development. Here’s what your journey will look like with a team of digital transformation professionals-
 Initial Consultation
Initial Consultation
Start by scheduling an initial consultation with the software development company. This is where you’ll discuss your specific security needs, goals, and any existing challenges within your network infrastructure.
 Requirement Gathering
Requirement Gathering
The development team will dive deep into understanding your requirements, gathering detailed insights into your network architecture, existing security measures, and future scalability needs.
 Design and Planning
Design and Planning
With a clear understanding of your requirements, the team will begin designing the blueprint for your network security management software. This involves mapping out the user interface, defining features, and planning the overall development process.
 Development and Integration
Development and Integration
Once the design is finalized, the development team will start building the software, integrating advanced technologies like AI, ML, and IoT to enhance its capabilities.
 Testing and Quality Assurance
Testing and Quality Assurance
Rigorous testing is conducted to ensure your software performs flawlessly under various conditions. This includes vulnerability testing, performance testing, and user acceptance testing to iron out any bugs or issues.
 Deployment and Launch
Deployment and Launch
After thorough testing and refinement, your network security management software will be ready for deployment. The development team will oversee the installation and configuration process, ensuring a smooth transition to the new security management system.
 Post-Launch Support and Maintenance
Post-Launch Support and Maintenance
The journey doesn’t end with the launch. The development company will provide ongoing support and maintenance services to ensure your new solution for network management remains up-to-date and effective in combating emerging cyber threats.
Choose Matellio for Network Security Management Software Development
When it comes to safeguarding your network, you need a partner you can trust. That’s where Matellio comes in. With our track record of delivering cutting-edge software solutions, we’re your go-to choice for network security management.
Why choose us? Simple. We’re not just another software development company – we’re your allies in the fight against cyber threats. Our team of experts is armed with the latest tools and technologies to build a custom solution that meets your exact needs.
With Matellio by your side, you can rest easy knowing that your network is in good hands. From seamless integration of advanced technologies to thorough testing and ongoing support, we’ve got you covered every step of the way.
So, if you’re serious about protecting your digital assets, don’t settle for anything less than the best. Choose Matellio for your network security management software development needs. Fill out this form to collaborate with us and seek the most advanced level of protection for your network.
Frequently Asked Questions (FAQs)
[sp_easyaccordion id=”49730″]